EXECUTIVE SUMMARY
As concerns over information security continue to increase, a growing number of business partners, customers, regulators, and other stakeholders require the organizations they do business with to demonstrate that the organizations have a sound information security management system (ISMS) in place. The most widely recognized data security standard is ISO/IEC 27001. Increasingly, having ISO/IEC 27001 certification is essential for doing business with many leading enterprises globally.
Our proven methodology over many years of projects will save your team months of effort in implementing ISO/IEC 27001 and making a workable plan to achieve it. And our experts guides you through all things needed to come into full compliance with ISO/IEC 27001.
Once this project is completed, You will achieve the following goals:
ㆍIdentification and risk assessment of all information assets
ㆍSecurity Vulnerability Test and Penetration Test for Information Systems
ㆍISMS Assessment and Implementation in accordance with the ISO/IEC 27001 requirements
ㆍISO/IEC 27001 Certification Audit of Global Certification Body (optional)
SERVICE STRATEGY
Our strategies to achieve successful ISO / IEC 27001 certification based on many years of experience and know-how is as follows.
A. Professional Consultant T / F Team Composition
– Consists of ISO / IEC 27001 Lead Auditor, Auditor qualification consultant
– Many years of experienced staff in ISO / IEC 27001 ISMS Assessment and Implementation
– Experts of security vulnerabilities and Penetration Testing technicians in various industries
B. Integration with Global Certification Body
– Proposal including Certification Body Auditing to overcome Initial Audit failover
– Certification acquired in a short period of time (minimum 3 months)
C. Know-how and technology transfer in project process
– Establishing consensus with stakeholders through training on ISO / IEC 27001 certification
– Technical transfer of technical security including security vulnerability testing
METHODOLOGY
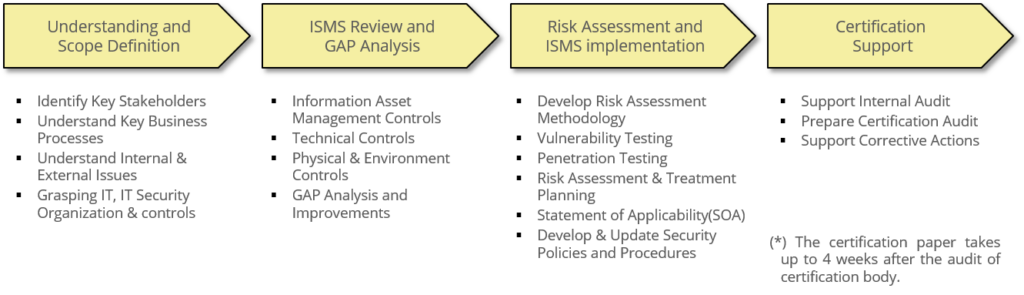
The consulting methodology consists of 4 phases from Understanding to Certification Support. Depending on the scope of project, there are a little bit deference tasks and steps of each phase.
※ Deliverables
Scope Statement, GAP Analysis, Information Asset Inventory, Penetration Testing Report, Vulnerability Testing Report, Risk Assessment Methodology, Risk Treatment Plan, Internal Audit Plan & Results, Statement of Applicability(SOA), Information Security Policies & Procedures, ISO/IEC 27001 Training Materials, Corrective Plan, etc.
CERTIFICATION PROJECTS ACHIEVEMENTS
In 2018,
KT Rwanda Networks ISO/IEC 27001 Certification Consulting — KT, Telecom(Overseaes)
’18 K-ISMS Certification Operation Consulting — SK Onestore, SK Group Company
In 2017,
’17 Vulnerability Analysis / Evaluation Consulting — Shinhan Investment Corporation, Shinhan Financial Group
‘17 K-ISMS Certification Operation Consulting — Shinhan Investment Corporation, SK Group Company
K-ISMS Certification Surveillance Consulting — Seoul ST. Mary’s Hospital, Airline/Medical
K-PIMS Certification Consulting — KOEN Co., Ltd., Public/Administration
ISO/IEC 27001 Initial Certification Readiness Consulting — NHN Entertainment Corporation, Game Company
In 2016,
’16 K-ISMS Certification Surveillance Consulting — SK Onestore, SK Group Company
’16 Vulnerability Analysis/Evaluation and Certification Consulting — Shinhan Investment Corporation, Shinhan Financial Group
’16 Daelim Corporation K-ISMS Certification Consulting — Daelim Corporation, Daelim Group Company
ISO/IEC 27001 Certification Upgrade Consulting — Daewoo Engineering & Construction, Construction
’16 K-ISMS Certification Surveillance Consulting — SK Onestore, SK Group Company
Website Vulnerability Testing (ISO/IEC 27001 Surveillance) — KTNET, Public Institutions
Website & MoblieApp Vulnerability Testing (K-ISMS, K-PIMS) — SK Telink Co, Ltd., SK Group Company
In 2015,
Security Vulnerability Diagnosis (K-ISMS) — Hanwha General Insurance Co., Ltd., Financial Company
ISO/IEC 27001 Certification Surveillance Consulting — Nanumlotto Inc., Manufacturer
K-ISMS Certification Surveillance Consulting — KT, Telecom Company
ISO/IEC 27001 Certification Surveillance Consulting — Daewoo Engineering & Construction, Manufacturer
Infrastructure Security Testing (K-ISMS) — SKB, ISP Company
In 2014,
LG Electronics Overseas Corporation ISO27001, BS10012 Certification Consulting — LG Electronics, Group
’14 K-ISMS Certification and Infrastructure Testing Consulting — KT, Telecom Company
K-ISMS Certification Consulting (including MobileApp Vulnerability Testing) — Tricycle, Financial Company
Certification(ISO/IEC 27001, PCI-DSS, K-ISMS) and Reguler Vulnerability Testing — BC Card, Credit Card Company
K-ISMS Certification Surveillance Consulting — Seoul Madical and Science Labortory, Healthcare
In 2013,
ISO/IEC 27001 Initial Certification Readiness Consulting — Daewoo Engineering & Construction, Online Shopping Mall
K-ISMS Initial Certification & Technical Protection Consulting — YES24, ICT Company
K-ISMS Consulting and Vulnerability Test — KTN, Telecom Company
In 2012,
’12 Second half Vulnerability Test (ISO/IEC 27001, K-ISMS, PCI-DSS) — BC Card & Construction, Credit Card Company
Korea Sports Promotion Foundation General Consulting (K-ISMS) — Korea Sports Promotion Foundation, Public Institutions
Korearatings K-PIMS Certification Consulting — Korea Ratings, Financial Company
Yonsei University Health System ISO/IEC 27001 Initial Certification Consulting — Yonsei University Health System, Healthcare
Shinhan Aitas ISO/IEC 27001, BS10012 Initial Certification Consulting — Shinhan Aitas, Shinhan Financial Group
In 2011,
ISO/IEC 27001, K-PIMS Certification Readiness Consulting — Daesang Group, Daesang Group Company
ISO/IEC 27001 and BS10012 Initial Certification Consulting — Shinhan Finace Invest, Shinhan Financial Group
ISO/IEC 27001 and BS10012 Initial Certification Consulting — Shinhan life, Shinhan Financial Group
ISO/IEC 27001 and BS10012 Initial Certification Consulting — Shinhan Capital, Shinhan Financial Group
ISO/IEC 27001 and BS10012 Initial Certification Consulting — Jeju Bank, Shinhan Financial Group
ISO/IEC 27001 and BS10012 Initial Certification Consulting — Shinhan BNP, Shinhan Financial Group
ISO/IEC 27001 and BS10012 Initial Certification Consulting — Shinhan Credit information, Shinhan Financial Group
ISO/IEC 27001 Certification Readiness Consulting — LG Inotek , LG Group Company
PROJECT CASE-1
Client :
KT Rwanda Networks Ltd. (in Rwanda)
Project Scope : (completed)
All the necessary tasks for obtaining ISO/IEC 27001 certification (including certification audit of certification body)
Main Activities
– [SD] ISMS scope Definition
– [RM] Risk Assessment and Treatment (including Vulnerability Test and Penetration test)
– [IM] ISMS Implementation and Training
– [OE] Operation and Performance Evaluation
– [CS] Certification Support
Deliverables
– About 18 Mandatory Documents and Records
– About 20 non-mandatory Documents and Records
Peculiar Activities
– Educating and cooperating on ISMS review and improvements
– Training and sharing the testing role on Security Vulnerability Testing
– Know-how and technology transfer in all project process
PROJECT CASE-2
Client :
Daewoo Engineering & Construction (in Korea)
Project Scope : (completed)
All the necessary tasks and documents for obtaining ISO/IEC 27001 certification (including certification audit of certification body)
Certification Background :
ISO/IEC 27001 certificate is required to strengthen competitiveness of overseas construction business
Main History(with our consulting service)
– in 2013, Initial Certification
– in 2015, Surveillance Certification
– in 2016, Upgrade Certification(version 2013)
Peculiar Activities
– Minimize the scope of certification with “Operate of IT Infrastructure”
– Provided readiness consulting service for certification preparation every year after obtaining initial certification
– Provide technical assistance for security hardening against vulnerabilities found in the technical vulnerability test
